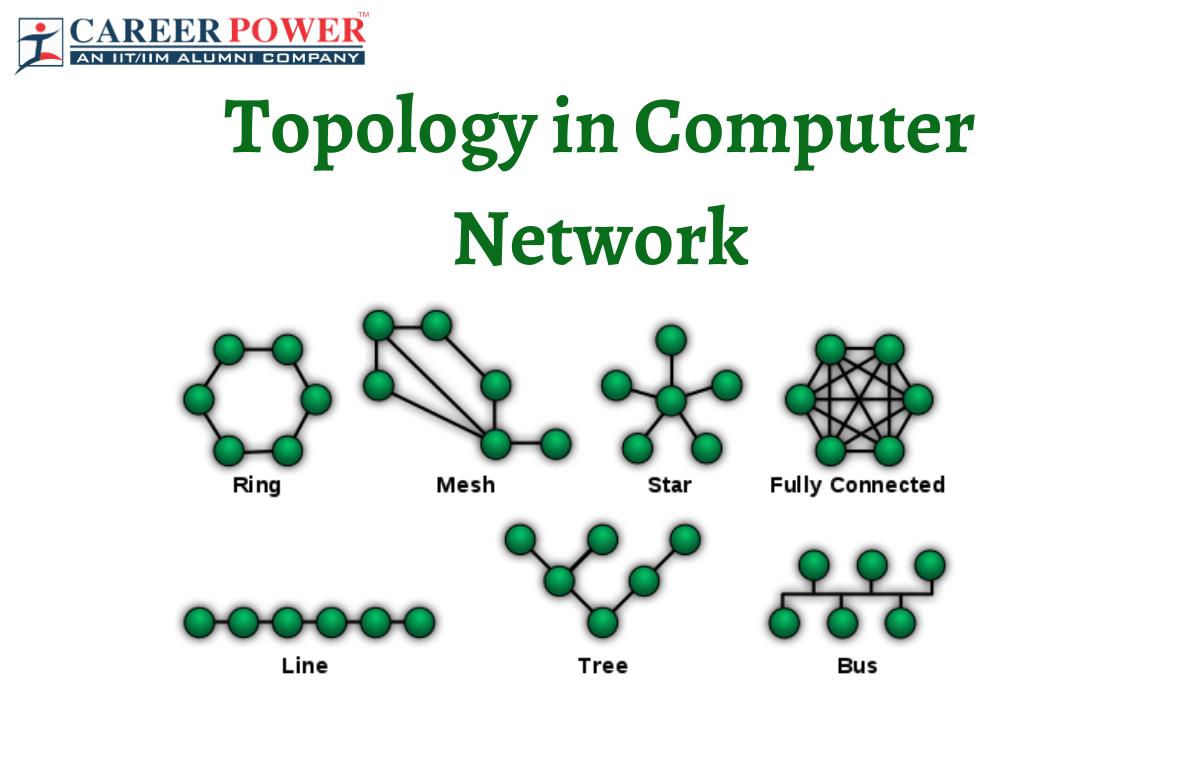
Topology in Computer Network
There are various ways through which different components are connected to one another in Computer Networks. The structure of the network of how all the various elements such as links, nodes, etc of a computer network are interconnected to each other is defined as Topology in Computer Network. The network topology can be classified into two categories-
1) Physical Topology: The placement of the various components of a network including device location, cable installation, etc is known as Physical Topology.
2) Logical Topology: The illustration of the flow of data within a network regardless of the Physical design is termed as Logical Topology.
Types of Topology in Computer Network
Network Topology is the arrangement of a network that comprises nodes and connecting lines via sender and receiver. There are 7 types of Topologies in computer networks namely Bus, Tree, Mesh, Ring, Star, Hybrid Topology and Point to Point Topology. Here in this section, we have discussed all the topologies in detail along with their advantages.
1. Bus Topology
In Bus Topology, all the stations are connected through a single cable known as a backbone cable. Every node of the network is either connected to the backbone cable by drop cable or directly to the backbone cable. In case a message has to be sent over the network, the message is put all over the network. The message will be received by all the stations available in the network irrespective of the fact that is has been addressed or not. The backbone cable is the “single lane” through which the message is broadcasted to all the stations.
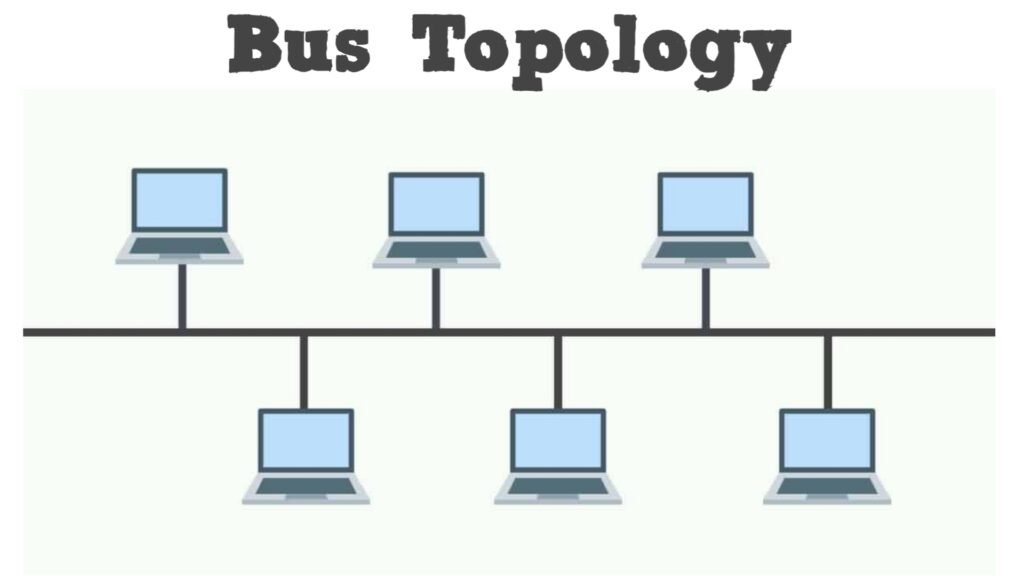
CSMA: The Carrier Sense Multiple Access (CSMA) is a media access control used to control the data flow so that data integrity is maintained and the packets do not get lost. The problems that occur when two nodes send the messages simultaneously can be handled via two alternative ways-
- CSMA CD: The access method used to detect the collision is known as the Carrier Sense Multiple Access Collision detection (CSMA CD). The sender stops transmitting the data once the collision is detected. Hence, it works on “recovery after the collision”.
- CSMA CA: The access method used to avoid the collision by checking whether the transmission media is busy or not is known as Carrier Sense Multiple Access Collision detection (CSMA CA). The sender waits until the media becomes idle if the transmission media is busy. This technique does not work on “recovery after the collision” and effectively reduces the possibility of the collision.
Advantages of Bus Topology:
- The nodes in the bus topology are directly connected to the cable without passing through a hub making the initial cost of installation low.
- The installation and troubleshooting techniques are well known and the hardware components are also easily available because of the bus topology being a familiar technology.
- Failure in one node cannot affect the working of other nodes.
- In Bus topology, coaxial or twisted pair cables are mainly used that support up to 10 Mbps.
- CSMA is the most common method used for this type of Topology.
2. Ring Topology
The Ring topology is somewhat the same as the bus topology, but with connected ends. The node that receives the message from the previous computer is responsible for transmitting it to the next node. The data that flows is unidirectional, and flows in one direction. The data flows in a single loop continuously which is known as an endless loop. Each node is connected to another node having no termination point. The data in the ring topology flows in a clockwise direction.
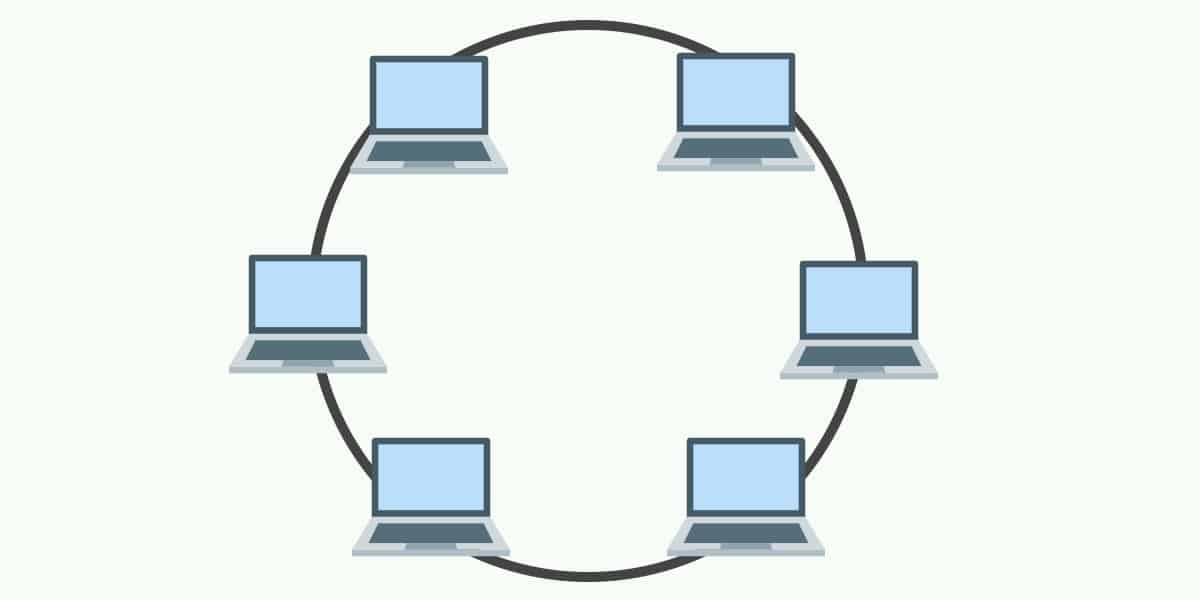
Token Passing: The most common accessing method of the Ring Topology is Token Passing.
- Token Passing: The network access method in which a token is passed from one node to another node is called Token Passing.
- Token: The frame that circulates around the network is known as Token.
Working of Token Passing: A token is passed from computer to computer moving around the network until it reaches the destination. The token is then modified by the sender by putting the address along with the data. This data is then passed from one device to another until the destination address matches. The token is sent for acknowledgment to the sender once received by the destination device. A token is used as a carrier in Ring Topology.
Advantages of Ring Topology:
- In Ring Topology, the faulty devices can be removed from the network without affecting the whole network.
- Many Hardware and Software tools for network operation and monitoring are available.
- The installation cost is very low because of the easy availability and usage of twisted pair cables.
- Since the communication system is not dependent on a single host computer, it is more reliable network.
- The transmission of data in speed in this topology.
3. Star Topology
Star topology is the network topology in which all the nodes are connected to a single hub, switch, or central computer through a cable. The central hub is known as “Server” and the other connected nodes are known as “Clients”. The hub can be intelligent which is known as the “Active hub” while the non intelligent hubs such as broadcasting devices are known as “Passive Hub”. The computers are connected using the Coaxial cable or RJ-45 cables. Star topology is the most popular topology in network implementation.
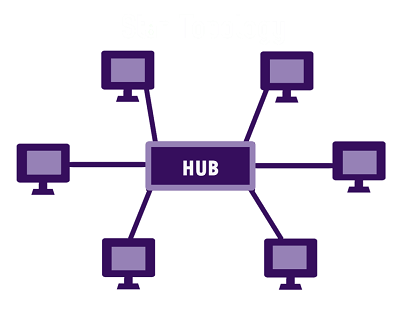
Advantages of Star Topology:
- Star Topology easily implements the complex network control features. It also easily accommodates any changes made in the topology.
- Troubleshooting is very efficient in Star Topology as the devices are connected to a single hub so the administrator has to directly go to the single station to troubleshoot the problem.
- Failure in one cable does not effect the network as each device is directly connected to the central hub with its own cable.
- Star topology is a familiar technology as its tools are cost-effective.
- This network topology is easily expandable as the new stations can be added to the open ports on the hub.
- The usage of coaxial cables make this network topology cost effective and inexpensive.
4. Tree Topology
Tree Topology is a combination of the characteristics of Bus and Star topologies. All the computers are connected with each other in a hierarchical fashion in a Tree Topology. The topmost node is known as the “Root node” while all other nodes are the descendants of the Root node. This topology forms a parent-child hierarchy as there is only one path that exists between two nodes for the transmission of data.
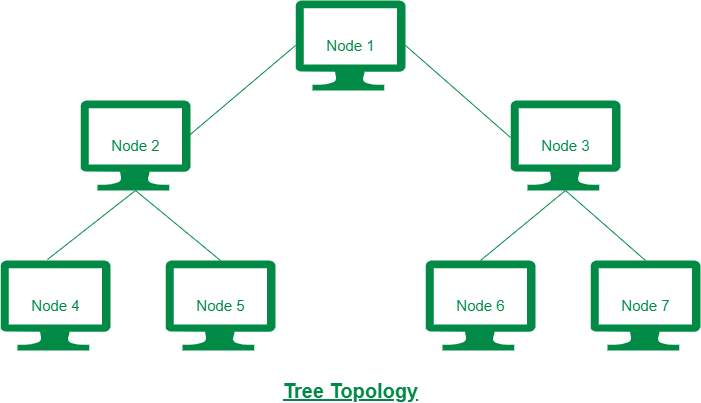
Advantages of Tree Topology:
- We can easily add a new device to the existing network to expand the network.
- This topology is used to send signals over long distances and used to provide broadband transmission.
- The Tree Topology enables the error detection and correction to be done easily.
- The whole network is not affected by a breakdown in one station.
- The entire network is divided into segments known as star networks which are easily managed and maintained.
- Tree Topology has point-to-point wiring for individual segments.
5. Mesh Topology
The arrangement of the network in which all the components are interconnected with each other via dedicated channels are known is known as Mesh Topology. This network topology does not have any switch, hub or central computer as a central point of communication. The most common example of Mesh Topology is the Internet. WAN implementation is used for this topology which makes communication failures a critical concern. These are mainly used for wireless networks.
This topology can be formed using the formula- Number of cables = (n*(n-1))/2
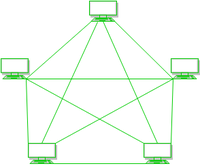
Mesh Topology can be divided into two categories-
- Full Mesh Topology: Each computer is connected to all the computers available in the network in a Full Mesh Topology.
- Partial Mesh Topology: In a Partial Mesh Topology, only certain computers and not all of them are connected to those computers with which they communicate frequently.
Advantages of Mesh Topology:
- Mesh Topology enables fast communication between the nodes.
- Expansion of the network by adding new devices will not disrupt the communication between other devices.
- This network topology is very reliable as the communication between connected computers is not affected by any link breakdown.
- Mesh Topology provides security and privacy.
- Any fault or error in the network is easily diagnosed.
6. Hybrid Topology
The Hybrid Topology is a combination of various different topologies. In this topology, a connection is built between different links and nodes to transfer the data. A Hybrid Topology is only formed when two or more different topologies are combined together but if similar topologies are connected together, it will not form a Hybrid Topology. For example- If in case there exist a bus topology in one branch of ICICI Bank and a Ring topology in another branch of ICICI bank, the connection of these two topologies will result in a Hybrid topology.
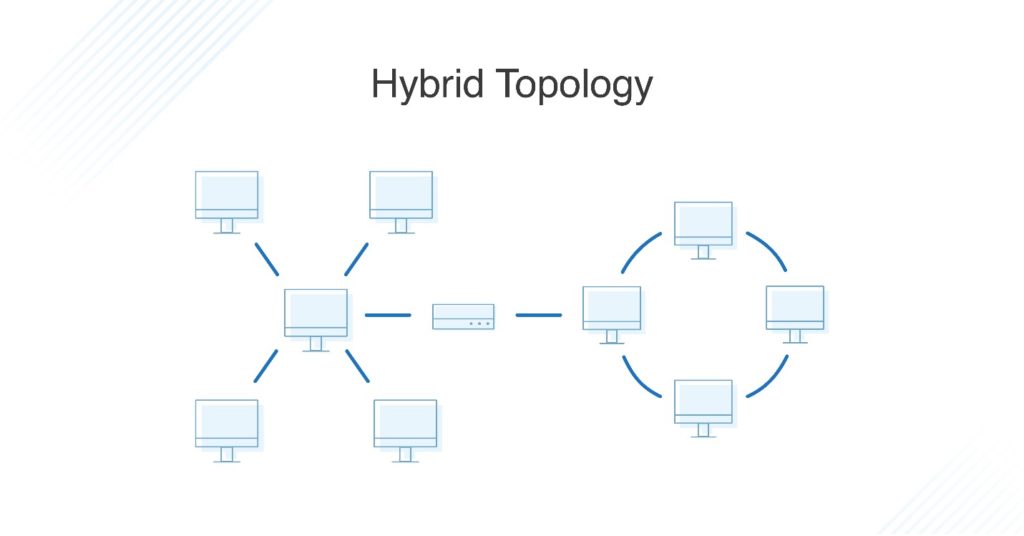
Advantages of Hybrid Topology:
- The Hybrid Topology provides flexibility as it can be easily designed according to the needs of the organization.
- This topology is very effective as it can be designed so that the strength of the network is maximized and the weakness is minimized.
- Hybrid Topology can be easily expanded by adding new devices to the network without affecting the existing network.
- The functioning of the network is not affected if any fault occurs in any part of the network.
7. Point to Point Topology
The Point to Point Topology is the simplest form of topology as the functionality used in it is of the sender and the receiver. This is the simplest form of communication as there is no mediator in-between, just the two nodes in which one is the sender and the other one is the receiver.






 Generation of Computers 1st, 2nd, 3rd, 4...
Generation of Computers 1st, 2nd, 3rd, 4...
 Input Devices of Computer: Definition, F...
Input Devices of Computer: Definition, F...
 Computer Languages and it's Types
Computer Languages and it's Types